The Long Tail of IoT and How We Handle It
There’s the perennial joke that the “S” in IoT stands for “Security”. With cases like the recent spate of WD storage appliances being wiped on mass, which turned out to be an old, but critical Remote Code Execution (RCE) vulnerability, the question remains unanswered – how do we handle the long tail of IoT? Where appliances rely on cloud services or mobile apps, notifications can be sent to let users know the device they spent good money on is now defunct or end of life and open to the wilds of the Internet.
This may not even be an appropriate model in some cases. Consider the idea of a smart door lock. Are consumers really going to buy the next model if the life of their current purchase is artificially shortened? After all, deadbolts don’t stop working, even if the manufacturer no longer exists.
The WD storage appliance incident falls into a weird middle ground. The same place you find home routers that haven’t seen a patch since they left the factory. I’d assert most users install the devices and completely forget they exist until they stop working. Why should we expect them to? We don’t patch washing machines.

We could consider the idea of alerting users to the fact their appliances are no longer supported and thus vulnerable. The problem there becomes how. Would you really be happy with a small speaker installed into a storage appliance announcing end of support at 2am? I’d fear for the lives of whoever made such a decision. It’s in the same ballpark as a washing machine that announces you needed to upgrade by printing a pattern of dirt on your laundry – rather unwanted.
But this is where we come to a bit of an impasse. On one hand, I want to be able to buy an appliance and continue using it as long as it still works. I’d be properly angry if my car stopped working once it hit an arbritary age and I’m sure you would be as well. On the other hand, continued support for IoT appliance long beyond the expected lifetime is expensive. Someone has to build and deliver patches to these devices.
While subscriptions could pay for this, do you really want a subscription for every smart home device you pick up? The picture is a little different with the HVAC control system that comes with a support contract and a consumer that understands the risk of running the system beyond this end of this. I can’t imagine you’d be happy to be locked out of your smart thermostat in your house because you missed a payment.
Peleton took the risk in forcing consumers to have a live subscription to continue using their treadmills. They’re hoping a three month stay of execution and the vague notion of returning the device for a refund will placate customers. Actions like this stray into the even more political world of device ownership. Do you really own that smartphone you paid for? The software needed to run it is only licenced to you and could suddenly require a subscription at any time. The likelihood is that won’t happen but it’s possible.

The reality is that we will continue to use devices long beyond their expected lifetimes. This applies across the whole spectrum of IoT devices, no matter how smart or connected they are. After all, it can be the most economic and environmentally friendly thing to do.
Ideally these devices should be patched regularly but there has to be a sunsetting process – a way of informing users that their storage appliance will keep working but at their own risk. But even that feels not enough.
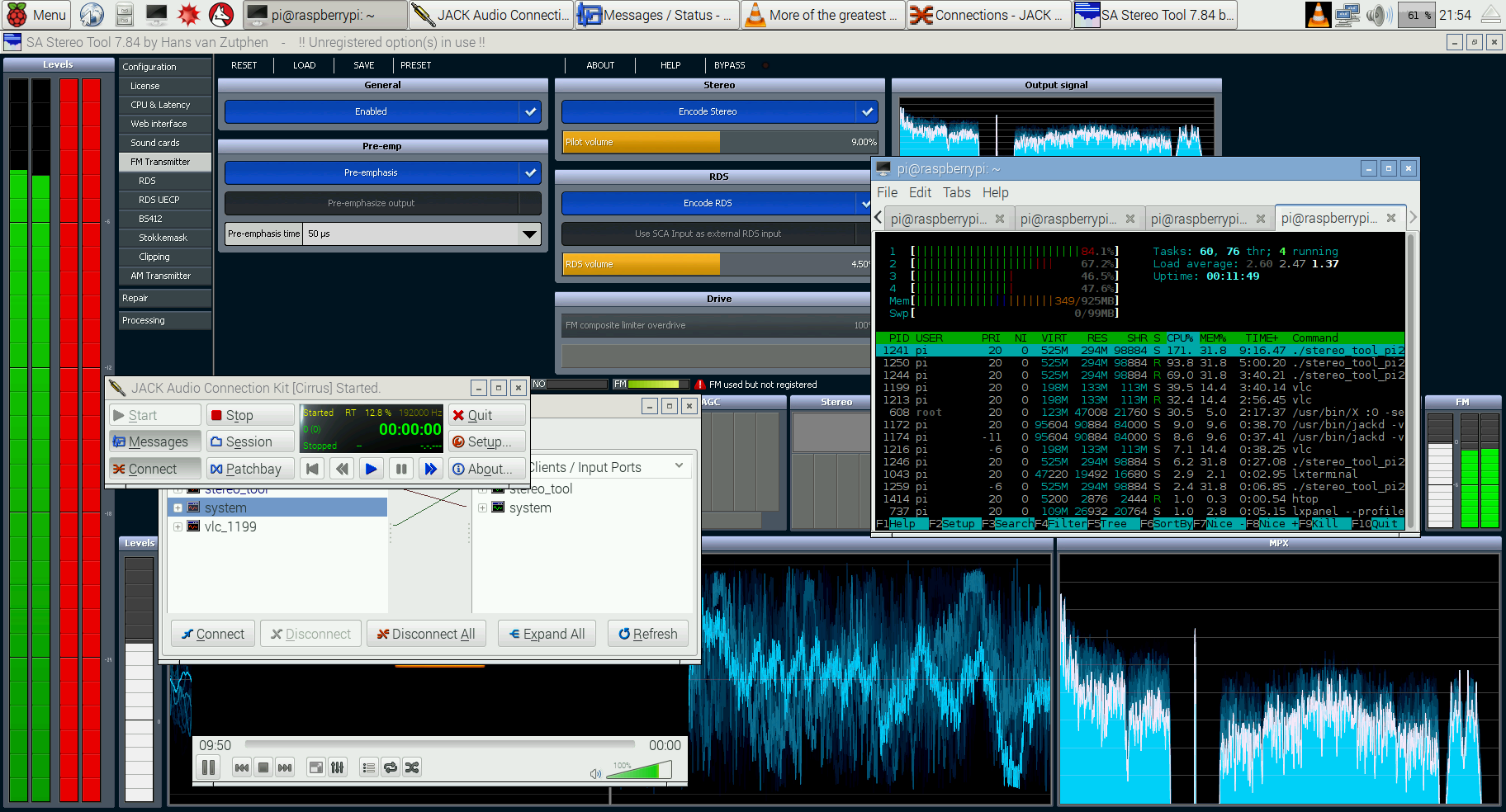
We can’t expect manufacturers to patch these things forever. Handing over to the Open Source community feels like a cop-out. While a lot of IoT appliances are just Linux boxes with a shim on top, which are written to a variety of quality levels, expecting the community to take on the burden of something a company made a profit on feels wrong.
What is the solution to the long tail? I don’t think there is one. But what I can say is this attack on WD appliances won’t be the last and we’ll see a lot more as IoT pervades even more of our lives.

Hi there
My name is Helen, I am the content editor @ wizcase.com
Thank you for publishing our vulnerability findings in your article here https://www.dlineradio.co.uk/articles/the-long-tail-of-iot-and-how-we-handle-it/.
We would like you to please include credit to the original research we published, (ArsTechnica.com credited us).
https://www.wizcase.com/blog/hack-2018/
Thank you very much,
Helen